The stack that makes encrypted compute real.
Niobium makes encrypted workloads practical by uniting the math, the hardware, and the environment into a single platform.


[ THE FOUNDATION ]
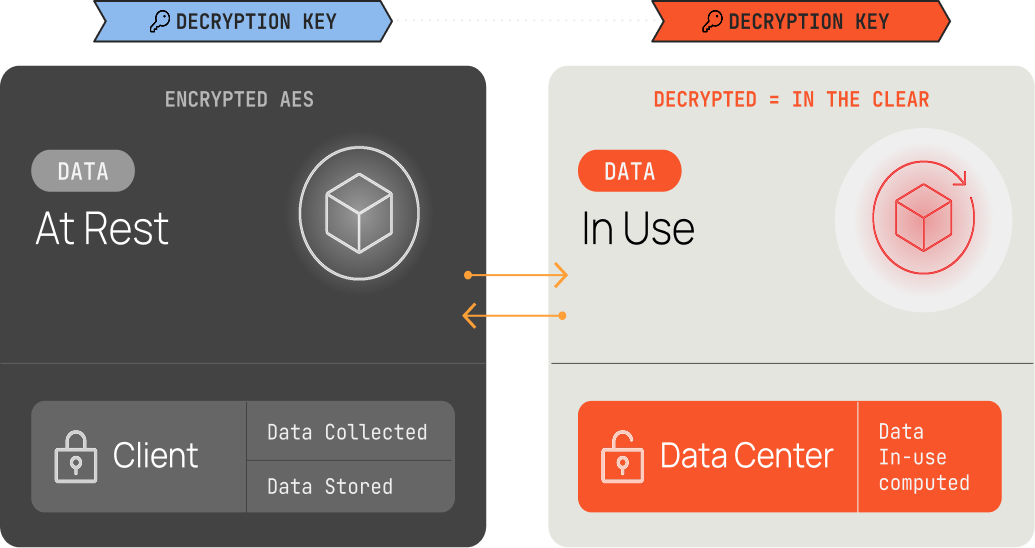
We’ve built niobium on Fully Homomorphic Encryption (FHE), so that data remains encrypted throughout computation. Trust is no longer required, it’s mathematically provable privacy.
Post-quantum secure
FHE is based on lattice-based cryptography, believed to be resistant to quantum computing attacks
Zero-trust architecture
The compute infrastructure never has access to plaintext, eliminating trust in the infastructure partners and compute provider
Client-side key management
Only you hold the private key. Fog has no key material
No “trusted” execution environments. decryption windows. exposure during processing.
TRADITIONAL COMPUTE
If encrypted computation never exposes data, why hasn’t everyone done this before?